Main PACS Server Demo Security AddIn
This Add-in implements Basic TLS Secure Transport Connection Profile of DICOM Standard which utilize the framework and negotiation mechanism specified by the Transport Layer Security Version 1.0 protocol. Any LEADTOOLS PACS Framework server service can be converted to use secure transport connection to provide protection against tampering, eavesdropping, masquerading by simply placing the add-in to the framework's server folder and configuring it. As for example, when router or proxy server need to accept images from remote PACS Client (resident on different geographic location) over the public internet connection, just copying the Leadtools.AddIn.Security.dll to C:\LEADTOOLS 19\Bin\Dotnet\Win32\L19_SERVER32\AddIns\ folder and configuring the certificates will add secure communication capabilities to the router server.
This add-in provides support for following areas of Basic TLS Secure Transport Connection Profile of DICOM standard:
- Computer or Entity Authentication - RSA based certificates
- Exchange of Master Secrets (RSA)
- Data Integrity - Secure Hash Algorithm (SHA)
- Privacy - Triple DES EDE, CBC
Security Icon - Double click on this icon from PACS Server Manage while L19_SERVER32 is selected to access the following security add-in options dialog to configure.
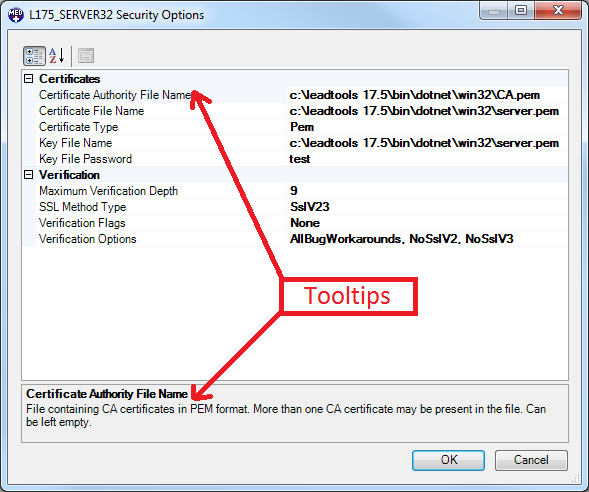
Certificates
- Certificate Authority File Name: Location of the Certificate Authorities digital certificates in Privacy Enhanced Mail (PEM) format.
- Certificate File Name: Location of the Server Certificate File in PEM format.
- Certificate Type: Select from dropdown list between Abstract Syntax Notation One (ASN.1) or Privacy Enhanced Mail (PEM) certificate type.
- Key File Name: File containing the private key. Server certificate file may also contain the private key.
- Key File Password: Password for private key if protected with a password.
Verification
-
Maximum Verification Depth: Maximum allowed depth of certificate chain from root certificate to be verified.
-
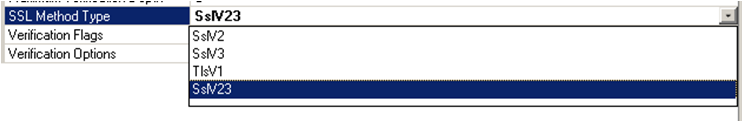
SSL Method Type: Select one of the SSL method type to be used for security verification from the drop down list.
-
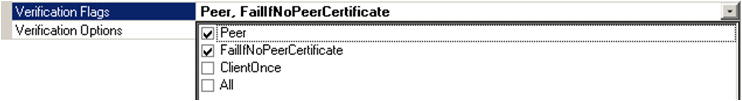
Verification Flags: Select one or more the verification mode to be used from the drop down list.
-
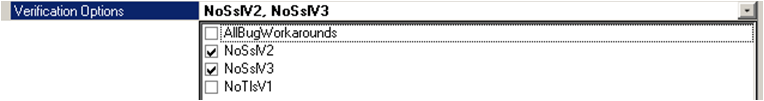
Verification Options: Select one of more additional options for verification mode from the dropdown list.
AddIns Project:
The C# sample project for Add-ins used in this server is located in <LEADTOOLS 19>\Examples\PACSFramework\CS\Sample AddIns\ folder
Add-in Runtime DLLs:
All runtime versions of Add-ins are in <LEADTOOLS 19>\Bin\Dotnet\Win32\L19_SERVER32\AddIns\ folder.
A copy is also stored in <LEADTOOLS 19>\Bin\Dotnet\Win32\PACSAddIns\ folder.
Note: The path of the source code for this binary is <INSTALLDIR>\Examples\PACSFramework\CS\Sample AddIns
© 1991-2017 Apryse Sofware Corp. All Rights Reserved.
